July 22, 2017
Next time you are at an airport, coffee shop, or public area with open Wi-Fi, think twice about connecting. These public wireless networks have become prime targets for hackers to steal your data and personal information, and it doesn't happen the way you might think.
Let's say you go to the local coffee shop to get some work done. You open your laptop and see a public wireless network with the coffee shop's name. You connect to the wireless network like you always do and now you are on the internet. First you check your personal bank account for balance details and you check your trading account and your 401k. Then you send an email to the head of your company with the latest on big merger agreement that's about to go through. The next day there are fraudulent charges on your bank account statement, and you turn on your TV and see news has leaked about the merger deal. Now you're sitting there wondering how could this could have happened?
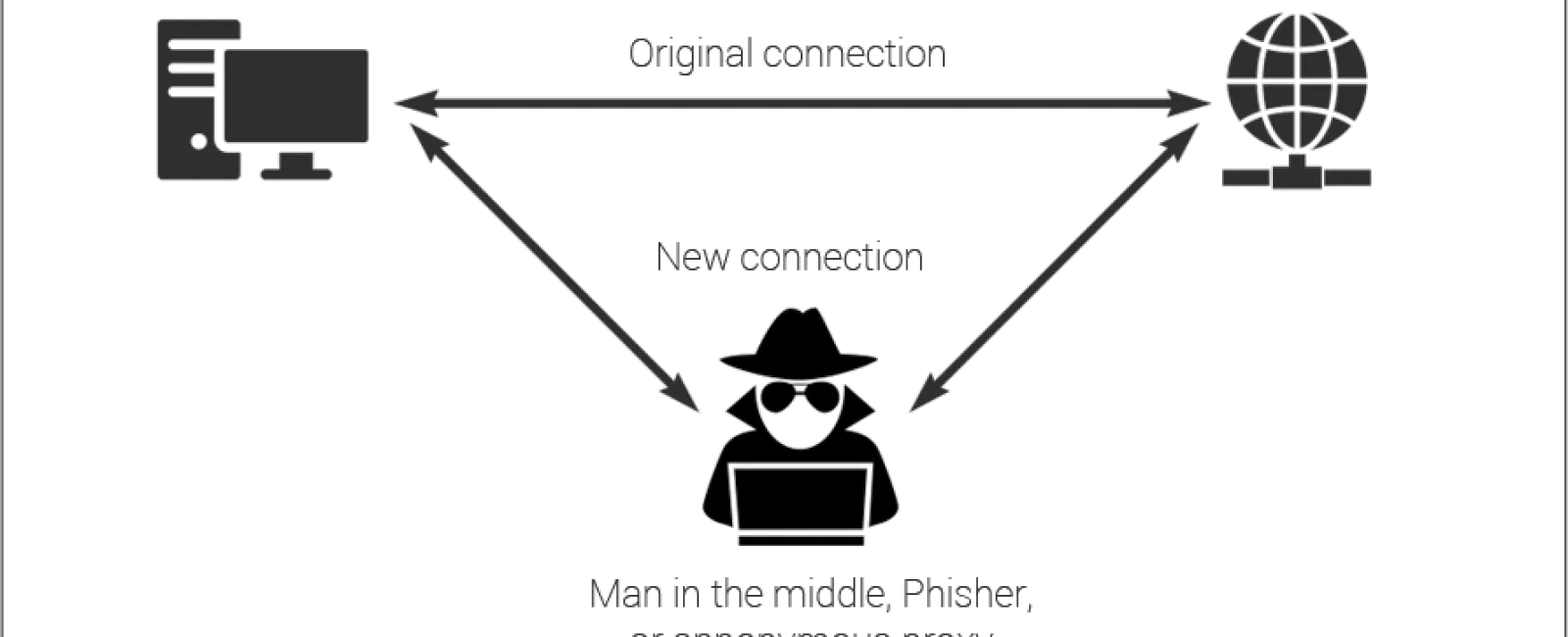
Well, you weren't actually connecting to the coffee shop's wireless network. A hacking technique called man-in-the-middle compromised your wireless security. The way it works is relatively simple. A rogue wireless device is setup near a public wireless network. This rouge device connects to the public wireless network and then re-broadcasts the name of the public wireless, masking itself as the trusted wireless network. When you connect to the wireless network you think you are connecting to the coffee shop's network, but you were actually connecting to the rogue device.
The device is able to see all network traffic that is transmitted to the internet while you're connected. This can be usernames, passwords, credit card data, and more. Even if the site or data is encrypted, it's able to decrypt all traffic that passes through and capture the data.
Here is a very funny clip from the show Silicon Valley about man-in-the-middle attacks.
https://www.youtube.com/watch?v=mK3CLAXpL6s
There are ways of protecting your systems and data from man-in-the-middle attacks. We recommend having an expert review your IT security systems. JNT TEK offers free security evaluations for organizations interested in an assessment.
Written By
JNT TEK
818-456-0626
jnt.wpenginepowered.com
sales@jnttek.com